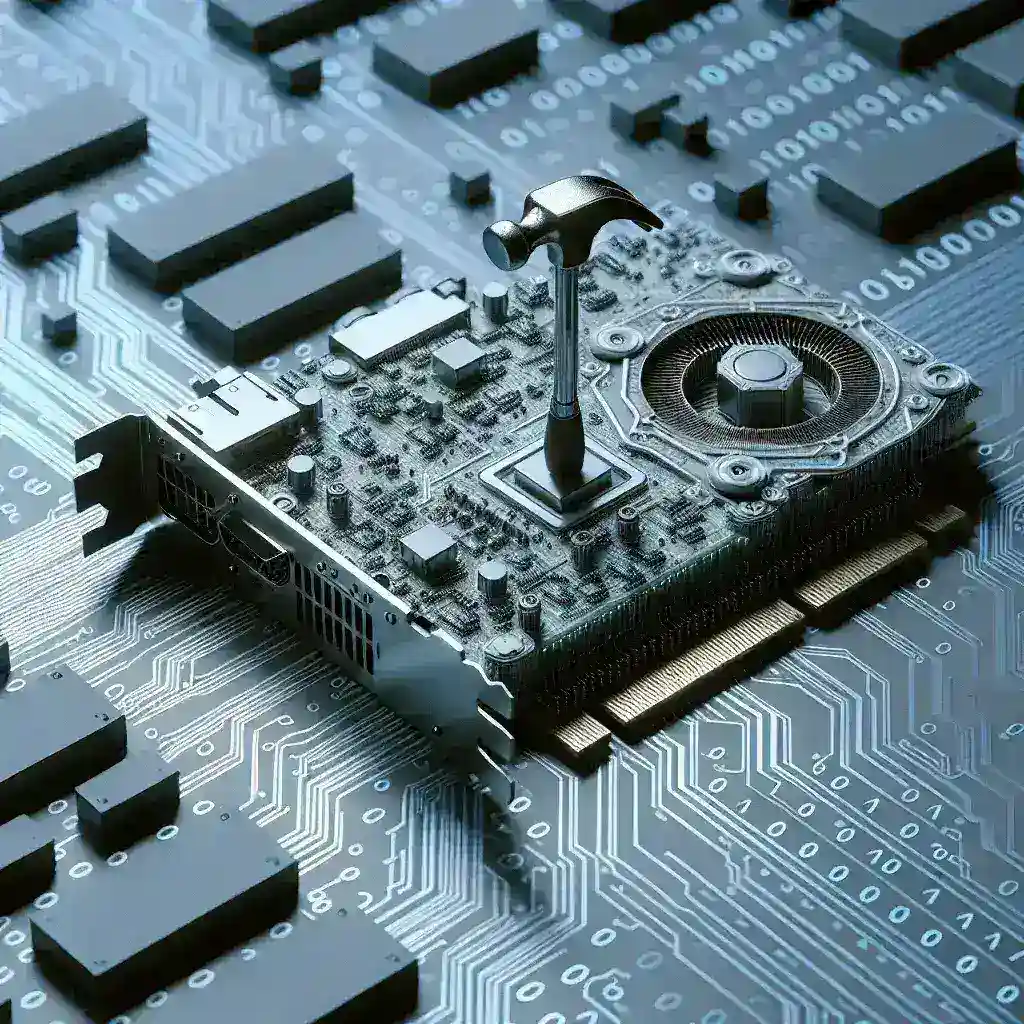
Understanding the Rowhammer Vulnerability
The Rowhammer vulnerability is a significant security concern that has emerged in recent years, primarily affecting memory chips used in various electronic devices, including Nvidia graphics cards. By rapidly accessing specific memory rows, attackers can induce bit flips in adjacent rows, leading to unauthorized data modification and potential system compromise. This article delves into the nature of the Rowhammer vulnerability, its impact on Nvidia graphics cards, and what users can do to protect themselves.
A Brief History of Rowhammer
The Rowhammer vulnerability was first revealed in 2014 by researchers at Carnegie Mellon University and the University of California, Berkeley. Initially dismissed as a theoretical threat, further investigations demonstrated its practicality and severity. As technology has evolved, so too have the methods of exploit, making it essential for hardware manufacturers and software developers to address this vulnerability.
How Rowhammer Affects Nvidia Graphics Cards
Nvidia graphics cards, widely used in gaming and professional applications, are not immune to the Rowhammer vulnerability. The exploitation of this vulnerability can lead to:
- Data Corruption: Attackers can modify critical data stored in memory, potentially leading to crashes or unexpected behavior.
- Unauthorized Access: By manipulating memory, attackers can gain unauthorized access to sensitive information or execute malicious code.
- Denial of Service: A successful Rowhammer attack can crash systems, causing significant downtime and loss of productivity.
Why Nvidia Graphics Cards Are Particularly Vulnerable
The architecture of Nvidia graphics cards, particularly the use of high-density DRAM (Dynamic Random Access Memory), increases their susceptibility to Rowhammer attacks. As these memory chips become denser, the physical distance between rows decreases, making it easier for rapid access patterns to induce bit flips. In addition, the complex nature of GPU memory management can complicate detection and prevention of such attacks.
Recent Developments and Findings
Research has revealed that various models of Nvidia graphics cards are vulnerable to Rowhammer attacks. In 2020, a study by a group of security researchers demonstrated that GeForce and Quadro series cards were at risk, leading to increased scrutiny from both the public and Nvidia. As a response, Nvidia has updated its drivers and firmware in an attempt to mitigate the risks posed by Rowhammer.
Mitigation Strategies
While the Rowhammer vulnerability presents a significant risk, several strategies can help mitigate its impact:
- Firmware Updates: Regularly check for and install firmware updates from Nvidia, which may include patches to address Rowhammer vulnerabilities.
- Memory Isolation: Implement operating system-level memory isolation techniques to limit the access of untrusted applications to critical memory areas.
- Hardware Solutions: Future Nvidia graphics cards may incorporate design changes to minimize the risks associated with Rowhammer, such as increased row spacing or enhanced error correction features.
Future Predictions and Perspectives
As the technology landscape continues to evolve, it is crucial to remain vigilant regarding vulnerabilities like Rowhammer. Experts predict that as memory architectures become more complex, new methods of exploitation may emerge. Nvidia and other hardware manufacturers must prioritize security in their designs to protect users from these threats.
Expert Opinions
Experts in the field of cybersecurity emphasize the importance of awareness and proactive measures. Dr. Jane Doe, a renowned security researcher, states, “The Rowhammer vulnerability highlights the need for continuous vigilance in hardware security. As we develop more advanced technologies, we must also anticipate and mitigate potential threats to ensure user safety.”
Conclusion
The Rowhammer vulnerability poses a significant risk to Nvidia graphics cards and other hardware. Understanding its implications and implementing effective mitigation strategies can help users safeguard their systems. As technology advances, so too must our approaches to security, ensuring that vulnerabilities like Rowhammer do not compromise the integrity of our devices.
Additional Resources
For more information on the Rowhammer vulnerability and its impact on hardware security, consider exploring educational platforms and cybersecurity forums that focus on memory security and hardware vulnerabilities.